131B-2 Python
DR CRYPTO "DR" <darwin_maring(at)hotmail.com> provides
an opening submission for this device.
"The B-2 machine, known as Python, was an enormous square box,
filled with relays was used with one-time tape. On this tape were a series
of keys. Keys were composed of groups of random Baudot characters.
At any given time, there were only two of these one-time tapes in existence,
worldwide. The transmit tape and the receive tape had a number printed
with an arrow every so many characters. That would delineate the
beginning of a new key.
The transmitting operator would inform the receiving operator which
key to use. As an example, the operator would type "Set 32" in plain text,
then both ends would put the arrow associated with the number 32 on the
set mark on the tape reader head. After a pause of several minutes
the transmitting operator would start typing the plain text to be encrypted.
If another circuit was available, it would be reserved for plain
text order messages. In this scenario, after the tapes were mounted in
the right spot, the receiving operator would send "32 Set" and communications
would commence on the secure line. Besides using the keyboard, messages
could also be provided in the form of punched paper tape thus resulting
in faster transmission time.
The key tape was provided on a really large reel akin to a movie
reel, and there was no limit on the length of the message. If the tape
ran out, operators would simply SET an new tape. When plain text messages
were provided on punched paper tape, it was mounted on a reader with a
dual head. The plain text and key tape would be read simultaneously to
produce the encrypted traffic.
To encrypt, modulus 2 was added without the carry to the character
which was typed and it incremented each time a new letter was typed
or a character read by a plain text tape reader. At the far end,
modulus 2 was added without the carry and the result was plain text.
It was very simple encryption and robust because there are no prime numbers
or any other set of numbers to generate it. It was strictly random
key and only 2 one-time tapes.
Because this machine was designed before the days of TEMPEST, no
consideration was given to the suppression of electrical noise emitted
by the relays in the B-2 and the taut heads (tape readers). Technology
eventually progressed to the point where the B-2's electrical emissions
could be read at some considerable distance thus hastening its service
life".
George Mace recalls his experiences with the B2 Table. "The
first and only B-2 Table I ever saw and worked on as a maintenance technician
was in the Joint Services Communications Center on "FRED" Island, Eniwetok
Atoll during the 1958 Nuclear Weapons Tests. It was in fact a large oak
desk, similar to those used by executives during WW-II. The Teletype printers
and transmitter/distributors (TDs) sit on the desktop. One TD for the clear
text traffic and one TD for the Crypto One Time tape.
Operational controls were on a front panel of the desk,
where normally the feet would go. Under the desk were numerous electro-mechanical
relays, inter-connected by all BLACK colored wire! I helped make point-to-point
ohmmeter checks of every wire in that beast. As far as I know, it was never
used for traffic during the 9 months I was there".
Read George's account of his posting to
Eniwetok Atoll.
Sid Carmean <sid_carmean(at)yahoo.com> also used the B-2. " I'll
throw in my memories of the B-2 table from the standpoint of an operator
in the USAF during my one-year assignment to Goose AB, Labrador in
1954-1955. We had three patchable full duplex circuits and we held
tape systems with Thule, Narsarssuak and Sondrestrom ABs in
Greenland as well as Pepperell and Harmon ABs in Newfoundland and
Andrews AFB MD, Loring AFB ME and Offutt AFB NE. These latter two
systems were for SAC operations as they rotated tankers and bombers on
TDY up north to train in the Arctic environment, just in case.
When they were operating, we were busier than usual.
I remember 'B-2' as being shorthand for the
manufacturer's model number '131B2'
and the Army/Navy nomenclature as being AN/FGQ-1 (Army) and CSP-2599(Navy).
And, as often as not, we referred to it as the "TAUT Table".
Curiously, or maybe not so, this device was absolutely unclassified,
as was the tape reader that read the cipher tape. Only the cipher
tapes were classified, at the SECRET level".
 |
|
 |
|
|
|
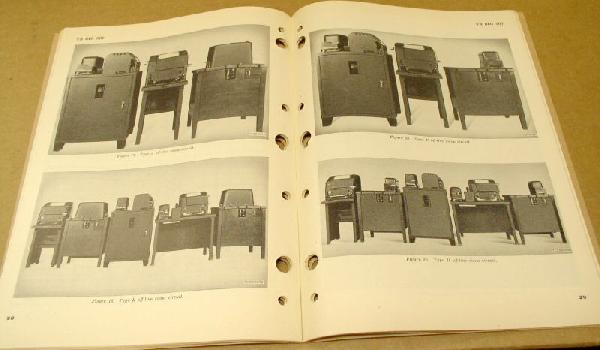
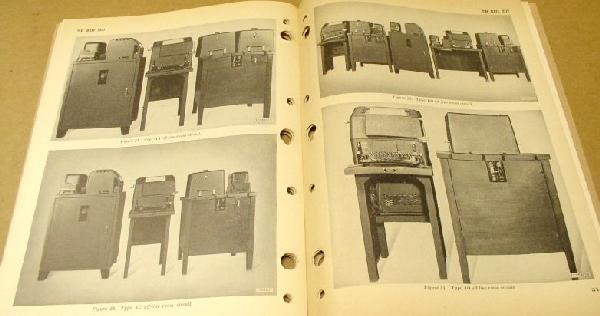
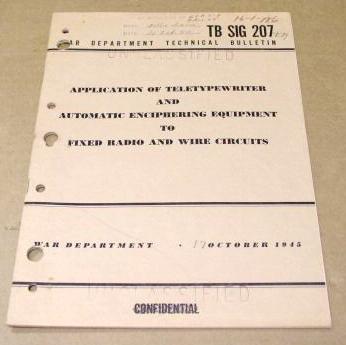
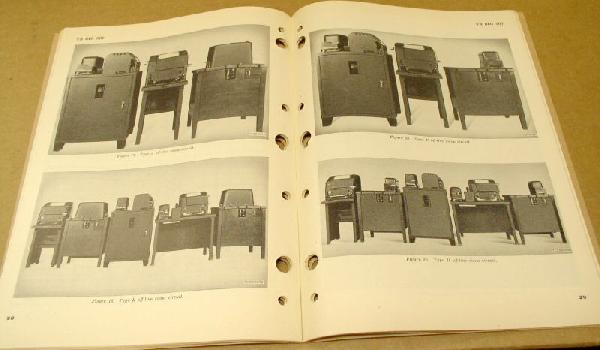
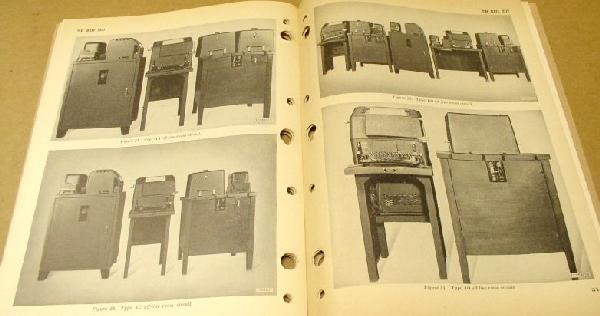
Sigtot variations from manual TBSIG207. (Submitted by George
Mace)
|
 |
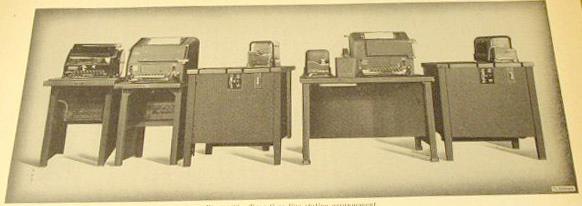
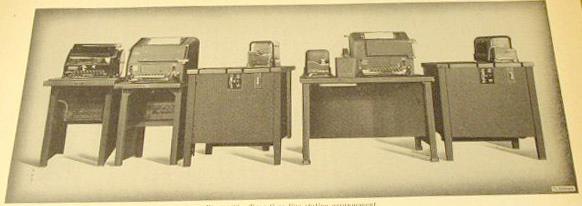
| General manual for SIGTOT equipment . (Submitted by George Mace) |
 |
| PP748/UM-1 power supply for use with "132B2" table which dates back
to 1946. The B2 would take two teletype tapes, one clear text and the other
random letters, exclusive OR (XOR) them together and send the resultant
output as secure traffic. (E-bay photo) |
 |
|
Power supply nameplate (E-bay photo)
|
Manual TM 11-2209 is applicable to the 131B2 Table.
Manual TM 11-5810-201-15P applies to the TSEC/HW-10 which was the
walnut coloured transmitter/distributor which read the One-Time-Tape for
this system as well as other one time tape systems.
While on the topic of long paper tapes, Doug Eyre offers this glimpse
into the 1960's world of punched paper tape.
"Known as nodes or hubs, various major sites around
the world routed data via secure teletype circuits. These sites were
known as P55(?) relay sites. Traffic was received and punched on Baudot
paper tape. This produced huge amounts of chad which was disposed of in
55 gallon drums! One of the famous tricks of the day was to fill a fellow
worker's tool box with chad.
Operators would take reels and reels of encrypted punched tape, read
the holes to determine the start of header then string them over to other
tape readers to be resent to outlying legs. Tension was kept on the tape
through spring loaded wheels. It kept the tape taut so that it wouldn't
hang up when it came out of the tape punch or when read by a tape reader.
Hence it became known as a taut head or taut tape relay.
Operators used to wrap the tape on their hands in a figure eight
between their thumb and little finger. Sometimes these could get
pretty big and were referred to as "footballs". You put the beginning
of the tape inside by your thumb and you wove it back and forth around
your thumb and little finger, crossing over in a figure 8 in the middle.
Then you could lay the football on the floor and pull the beginning of
the tape from the center and feed it into a tape reader and it would generally
flow flawlessly without getting tangled.
A relay site was known for bells and lights. When "FLASH" traffic
was received, operators had tape strung across the room literally from
the output of one tape punch to the tape reader relaying to another node.
The operator would guide the tape by hand to ensure that the message was
handled in super fast (for its day) time. An operator was expected
to be able to process a FLASH message in and out ot the relay site in less
than 5 minutes. Some operators colloquially known as tape apes could
take up to 1/2 hour to relay a message.
All of these messages were manually logged and there was no doubt
that it inflicted a great deal of stress on the operators. At Hickam,
we had between 80 and 100 different lines that were secured by the KW-26.
Many of those lines terminated in the P55 relay! Those men and women
that worked that relay site earned their money many times over. In
the chauvinist days, there were very few women in the crypto, teletype,
or radio (career) fields. However, they were great typists so the
majority of them worked in communications".
 |
Taken in 1980, this is an example of a small Communications Center
somewhere in Australia. On the right side of the room are Model 28KSR teletypes
and readers. Tape perforators, which produced a large amount of noise,
were fitted into sound-proof cabinets. At the left bottom is a Model 28KTR
Teletype. (Photo courtesy Syd Nagle) |
Ralph Irish, W8ROI, relates his experiences with crypto
gear while serving with the US Navy.
"I worked with PYTHON gear aboard the USS Hancock, a WW II Attack
carrier which was in service until the mid-70s. I made two 'cold war years'
cruises to the Western Pacific, in 1959-60 and again in 1960-61. Once we
got west of Hawaii things changed. We started using the KW-26 gear and
had the PYTHON as standby. The actual Crypto Center had two KL-47 Adonis
units, plus something called "VENUS". I only caught a glimpse of the VENUS
device on one occasion. It was quickly covered up by the Comm Officer using
it. The few seconds I did see I sort of indicated how it would be used,
but particular protocols and how to set it up for a decode were NOT obvious
in those few seconds.
On the second trip west, we relied heavily on the KW-26, the newly
added KW-32R and the PYTHON. WE had a flock of 'decode tapes' spooled on
red 7 or 8 inch spools, which sat on a spindle near the 'DECODE TD'. Incoming
tapes off the air were placed on the 'regular' or ordinary Model 14 TD.
The tapes were set to the start points and the switch set to "DECODE" and
the Model 14 TD was started. The plain text would show up on a Model 19
printer in most circumstances. We had two of them and one was carefully
behind the 'Green Curtain' which separated the rest or the TELETYPE room,
better known as the 'RATT Room". In that part of the room, there were a
number of receivers, AN/URA8A stacks, and a lot of 'patching equipment'.
The unclassified area of the RATT Room also had two Model 28s, a Model
14KTR, and most of the receivers and 'patching' equipment. That area monitored
the standard "Fleet Broadcast" on 60WPM TTY. Behind the curtain, we monitored
another 'Fleet Broadcast' of encrypted info which dumped data into a Model
28 with 100WPM gears. The first time I saw that machine running at full
speed, I mentally gave it about 3 months before it would fly apart. How
wrong I was! - - - - Toward the end of my final WesPac cruise, I heard
mentions of 'radiation' from the PYTHON system which could be read or interpreted
usefully from a distance. I did not have enough basic electronic knowledge
to fully understand the concept. One would think that the well known idea
of the 'Faraday Shield' could have been incorporated into the two TDs and
the other large box with all of the electronics and relay switching equipment.
Or an electrically isolated 'room' built for this equipment. I don't know
if the Main Crypto room had any special 'isolation' or not. Everything
there and along the outside walls of that room seemed quite ordinary to
me. Never thought to ask.
Anyway, all I can add to the PYTHON story is my own little experience
with it. All of our "Red spooled" decode tapes had the same master prefix.
Each spool had maybe 40 or 50 'spans' of punched tape before the next "Start
Number" showed. The "Start point" of the decode tapes was an inked line
across the tape, quite close to an inked number. the "Start point" of the
'off the air' tapes was the first character following two blanks, after
the normal header. I don't have a clue as to how many characters were on
each 'span'. I suspect that if I had paid too much attention to such things,
many eyebrows would have been raised and maybe my Crypto Clearance revoked.
Never can tell. All of that 'used' tape went into specially marked kraft
paper bags, and were designated as "Burn Bags", and a mid-senior NCO had
to be there at the 'burn point' supervising the addition of each such bag
to the flames, and stay around long enough to assure that everything had
been devoured by the flames. I recall being on a detail of hauling maybe
50 bags to that point, but I didn't have to stay around. In addition, there
were also 'Burn Bags' from the main Crypto Center, and I believe that everything
went at one time, as a certain amount of 'accumulation' took place".
Contributors and Credits:
1) Darwin Maring <darwin_maring(at)hotmail.com>
2) Don Robert House, N.S.E., Bell System Retired.
Curator Emeritus NADCOMM. email: k9tty(at)dls.net
3) Syd Nagle. <syd_tracy_nagle(at)iprimus.com.au>
4) Ralph Irish [w8roi(at)wowway.com]
Back To Menu
Page
Maa 15/19