CARD READER DESCRIPTION
Select this link to see the inside
of the card reader. Ronald Coppock, who worked with the KG-13
indicates that it was fitted with a card cutter and also without.
"In Ethiopia, I worked at two locations (Stonehouse and Tract C)
that had KG13's equipped with the KW26 style card cutters. All the machines
at Stonehouse were equipped that way and about 20% at Tract C. At the 7th
Radio Research in South East Asia, about 30% of the KG13's had the card
cutter style card readers. 13's equipped with the card cutters were operated
on very high priority circuits with short cycles to change key material.
Some were on 6 hour and others on 12 hour cycles".
The KG-13 did have a major difference in that in its latter years,
it was equipped with a Card Reader Insert Board or CRIB.
INTERNAL DESCRIPTION
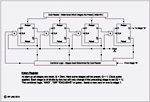
The KG-13 employed "FLYBALL" modules. These were modules
comprised of discrete components set up as logic element circuit groups
such as AND gates, OR gates, FLIP FLOPs, Inverters etc. Once tested,
the modules were potted in a compound whose colour indicated functionality.
The coloured potting compound was extremely hard and any attempt to penetrate
it resulted in damage to the internal circuitry.
In a KG-13, the following colours are confirmed: Pink, Yellow, Green,
Blue, Red, Orange and Black. Purple and Brown modules were probably used
but those colours are unconfirmed as of this time.
Failures usually occurred in the power supplies, buffers, and synchronizers
though most problems were quickly resolved. When new, there was a high
frequency of failures due to cold solder joints.
One board in the KG-13 had a black module which was a noise generator.
Repair depot technicians were told it was the only module which was classified
because the noise from a diode was used to generate a random key stream
used in the encryption process.
The circuitry inside the module then used the koken chains to create
an extremely random key stream. That was why there was no problem
in restarting the KG-13 with the same card. The noisy diode ensured that
the chances of duplicating the start point was not measurable by any standards
known at the time.
Two of the key cards were for the transmitter and the third for the
receiver. There were two for the transmitter because it had two key
generators. The keystream mixed with the plain text produced the
ciphertext. Two key generators generating the same keystream should
match bit for bit at the output and a mismatch would cause a crypto alarm
and a shutdown of the output. A key generator failure would stop
transmission and prevent a compromise. With only a single key generator
in the transmitter a failure could produce a trivial keystream (all one's,
all zero's or alternations). A receiver key generator failure just
produced garble. The KG-3 could be used to transmit or receive since there
is a XMIT/RECV switch on in the lower right hand portion of the lowest
unit.
In the 1964/65 time frame, crypto techs were taught that it would
take 50,000 years to break the key on a KG-13 using state of the art techniques
which were available at the time. The KG-13 also employed traffic flow
security.

|
|
A side profile of one drawer. (Photo by Bill Rhoads)
|
 |
| An internal view of one of the drawers showing the potted component
technique. (Photo by Bill Rhoads) |
To improve the reliability of the data stream, the KG-13 was used
in conjunction with the AN/FYC-3 (dubbed SHARQ). Fred Redick
expands on this. "It was an unclassified machine manufactured by
RCA and was deployed with the KG-13 on 100 wpm, point-to-point teletype
circuits leading to NSA. It also included the network of installations
that reported CRITIC [1] messages to NSA. A device about as large
as the KG-13, it was an automatic Error Detection and Correction machine.
The letters ARQ in the nick-name SHARQ stand for Automatic Request.
It added a cyclic redundancy check character periodically on the plain-text
side of the KG-13 and would notify the distant end SHARQ if an error was
detected in the data stream and automatically request that the affected
block of data be retransmitted. The SHARQ was controlling teletype
"step" (later known as clock) so the transmitting station stopped sending
while this error correcting process took place. This process took
a lot of garble out of otherwise raw TTY traffic. Training on the
SHARQ, even for Army folks, took place at Lackland AFB.
On later installations, when parts of the world-wide NSA CRITIC
network were being upgraded to 1200 baud high-speed service around
1970, the AN/FYC-3 was replaced with the AN/FYC-8, an IC based machine.
The internal temporary data storage of the AN/FYC-8 used the miraculous
but mercifully short lived technology known as delay line storage.
A delay line was a very long wire of a particular metallurgy that was crammed
into a metal box container in the machine. Data coming in one end
of the wire took a significant measurable time to get to the other end
of the wire plus somehow it was persistent while it was on that wire and
so if it wasnt invited out, it was effectively stored in the delay line".
KG-13's were taken out of service around 1989-90. This was one of
the last discrete component crypto machines built. Shortly after
this time, integrated circuits started to appear in crypto machine designs.
The machine depicted in the above phots was donated to the National
Cryptologic Museum Foundation by Bill Rhoads on 19 July 2004. An
illustrated article describing its arrival at the museum appeared in the
Spring 2004 issue of the NCMF internal publication, "The Link". As of 2010,
the KG-13 is in storage.
Also refer to Fascinator for complementary information.
FOOTNOTES:
[1] In mid-1958, a requirement arose for a reporting system that
could communicate critical intelligence from the field to the "highest
authorities" and with a response time not exceeding ten minutes.
A CRITIC message would include any item worthy of urgent attention, such
as indications of international crisis or impending military hostilities.
A CRITIC message could originate at almost any facility involved
with intelligence gathering. It could be from a large fixed station
operation with giant antenna arrays, large numbers of radio receivers and
data interpretation gear surrounded by scores of analysts. Alternately
it could be from a van on a truck in some forward position in a dangerous
area. A message with normal priority might take all day to get from
the field to a headquarters command. To get to the greater Washington DC
area, the total transmission time might be substantially longer.
A CRITIC message, therefore, was one with the most urgent priority.
The organizational determination to deliver was such that everything else
stopped when one was in the network. While in today's world it may
not seem remarkable to move a message half way around the world in under
ten minute's time but it was an astounding feat given the level of automation
prevalent in the 1960s. The establishment of this CRITICOMM system
made radical changes in the flow of critical intelligence to Washington.